Georgetown Security Lab
We investigate problems in computer security, network security, and privacy—building tools and theories that help people stay safe online.
Located in the Department of Computer Science at Georgetown University, the CS SecLab is an academic research group investigating problems in information assurance, computer security, programmable networks, and privacy.
Research Areas
Our work spans several interconnected areas:
Censorship Circumvention Network Security Privacy-Preserving Technologies Programmable Networks Usable Privacy & Security Cryptography Secure Distributed Systems
More information about our current work is on the Projects page.
Recent Highlights
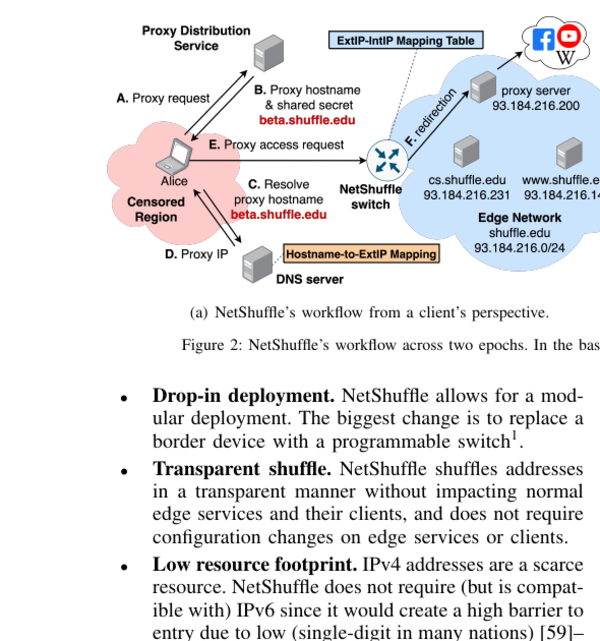
Shuffling Away Censorship at the Network Edge
NetShuffle repurposes commodity edge servers—the same infrastructure that delivers web content globally—as a distributed fleet of censorship-circumvention proxies. Because these servers are geographically dispersed and commercially essential, blocking them would cripple legitimate traffic, making censorship impractical.
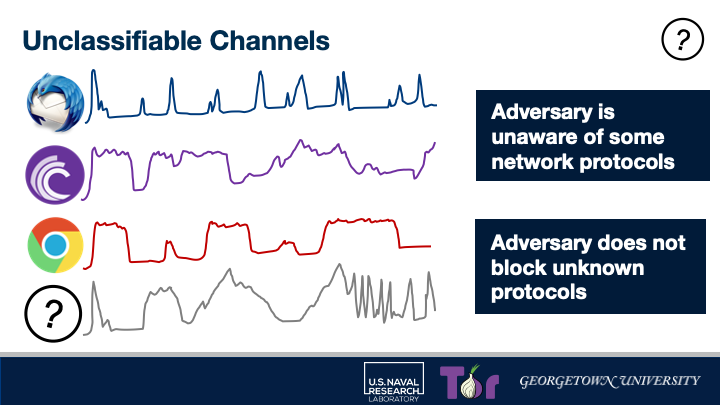
Evading Censors with Protocols They've Never Seen
Censorship filters block known protocols—but what if traffic looks like nothing in their classifier's training data? We show that generating network traffic that is statistically unclassifiable by deep-packet inspection is both practical and highly effective at evading real-world censorship systems.
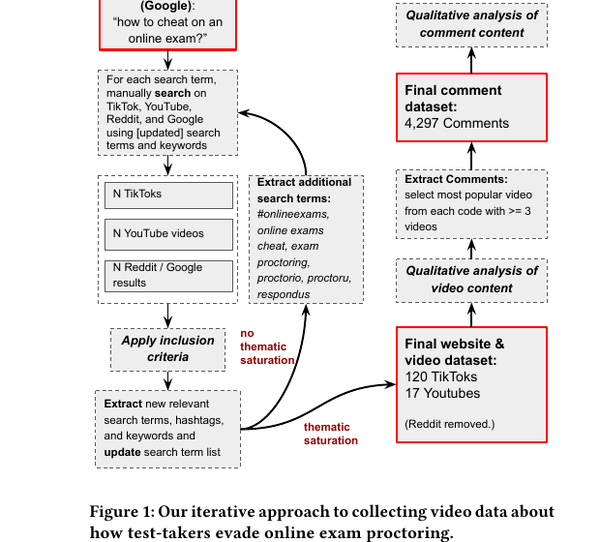
How Students Evade Online Exam Proctoring
Using iterative analysis of thousands of TikTok and YouTube videos, we document a rich community-developed playbook for defeating remote proctoring software—from browser extensions to VM tricks to phone stands. Our findings reveal how the adversarial cat-and-mouse game between proctors and students plays out in the open.
Joining SecLab
Current Georgetown students interested in security research should review the Projects page and contact affiliated faculty. Prospective graduate students should apply through the department’s regular admissions process and mention SecLab in their statement.
Mirage: Private, Mobility-Based Routing for Censorship Evasion (with Zachary Ratliff, Ruoxing (David) Yang, Avery Bai, Harel Berger, Micah Sherr, and James Mickens) presented at Network and Distributed System Security Symposium (NDSS), 2026.
Censorship Evasion with Unidentified Protocol Generation (with Ryan Wails, Rob Jansen, Aaron Johnson, and Micah Sherr) presented atUSENIX Security 2025.
Analyzing the AI Nudification Application Ecosystem (with Cassidy Gibson, Daniel Olszewski, Natalie Grace Brigham, Anna Crowder, Kevin R. B. Butler, Patrick Traynor, Elissa M. Redmiles, and Tadayoshi Kohno) presented at USENIX Security 2025.
Chimera: Fuzzing P4 Network Infrastructure for Multi-Plane Bug Detection and Vulnerability Discovery (with Jiwon Kim, Dave (Jing) Tian, and Benjamin E. Ujcich) presented at IEEE Symposium on Security and Privacy (S&P), 2025.
Reflexivity & Reflection (R&R) for Sociotechnical Safety: Creating a Space for Collective Learning (with Jessica McClearn, Lucy Qin, Emily Tseng, Miranda Wei, Rikke Bjerg Jensen, Nora McDonald, Elissa M. Redmiles, and Micah Sherr) accepted to CSCW 2025.
Co-Constructing the Future of Digital Intimacy (with Chris Geeng, Lucy Qin, Allison McDonald, Amna Batool, Diana Freed, Oliver L. Haimson, Jevan A. Hutson, Elissa M. Redmiles, and Micah Sherr) accepted to CSCW 2025.